We’ve all seen them in use. An employee approaches a gate or door, flashes a keyfob or access card, and they’re in. This is RFID (Radio Frequency Identification) access control in action. It’s one of the most widely used security technologies today, and it has revolutionized the way we manage access to our premises and equipment.
You might have even used them yourself in a hotel or at the office. But what makes RFID door access control so special?
In this article, we’ll explore the features and benefits of RFID access control, as well as its many uses.
What is an RFID door lock system?
An RFID door lock system is an automated access control system that uses radio frequency identification (RFID) technology to identify and authenticate users. It works by using a wireless signal from an RFID tag, keyfob, or card to unlock doors, gates, and other entry points.
That unique signal is sent to the door’s reader. The reader then checks the signal against its database of authorized users and if it finds a match, access is granted. This process happens in less than a second and requires no human intervention.
Types of RFID door access systems
There are three main types of RFID access control systems: active, semi-passive, and passive.
-
- Active systems use a battery to power the tag or card. They emit a signal that can be picked up by readers from several feet away — making them ideal for outdoor applications.
- Semi-passive systems use batteries to power the tags or cards but only send out signals when they come into proximity to an RFID reader. These are used more frequently indoors.
- Passive tags or cards draw their power from radio waves sent from the reader itself, making them perfect for access points that will have lots of authorized users, as it reduces the cost-per-user.
The most comprehensive security systems will often use a combination of these three access control technologies.

How much do RFID access systems cost?
The cost of RFID access systems will vary depending on the type and complexity of the system you need. Generally, active systems are the most expensive because they require more hardware and maintenance than other types. Semi-passive systems tend to be less expensive, while passive systems are usually the least costly option.
However, many other factors can affect the total cost of an RFID access system.
-
- Number of doors or entry points: The more entry points, the higher the cost.
- Number of users: More users will increase the cost of tags or cards.
- System features: Additional features such as temporary credentials, biometric authentication, or audit trails will add to the cost.
- System complexity: Complex systems with multiple access levels or remote monitoring capabilities can be more expensive.
With RFID access control systems, you get what you pay for. Investing in a quality system can save you money in the long run by improving security and reducing maintenance costs. Get connected with a local RFID integrator today to learn more about your options. Get Connected

How to install RFID access systems
Installing an RFID access system is a complex process that should be done by professionals.
1. Plan the layout
The first step is to plan out the layout of your system. This includes deciding which doors and entry points will be secured, as well as where readers and other hardware should be installed.
You’ll also need to decide what kind of RFID tags or cards you’ll be using. This will depend on the type of access control system you have chosen (active, semi-passive, or passive). Ask questions like:
-
- Do you need tags that can be used outdoors?
- Will they all use the same frequency?
- How many readers and tags do you need?
Once your plan is in place, it’s time to move on to the next step.
2. Purchase the necessary equipment
You’ll need to purchase the necessary hardware for your RFID access control system. This includes readers, tags or cards, power supplies, and other components.
Make sure you buy only genuine parts that are compatible with each other. It’s also important to keep track of what has been purchased and where it will be installed. Services like Proptia can help you to find the right products for your system, making sure that you get the best value for your money.
3. Install the reader hardware
Each access point that you wish to secure will need a reader. This is the device that will detect the RFID tag or card and grant access to authorized users. Several things require consideration.
-
- Weather: The reader needs to be able to withstand the elements, so make sure it’s in a sheltered area.
- Position: The device needs to be installed at a height that is convenient for users and secure from potential tampering.
- Connectivity: Make sure the reader has access to power and can communicate with other components like locks or alarms.
Once the reader is installed, you can move on to programming and configuring it.
4. Configure the reader settings
The reader’s settings need to be configured so that it can read the RFID tags and cards correctly. This includes setting up access levels, assigning permissions, and more.
Depending on your system, you may also need to set up an authentication server or connect to a cloud application for remote access control.
5. Program tags or cards
Programming the tags or cards involves assigning access rights to each user. You can also set up group access rights, allowing certain users to access multiple doors with a single tag or card.
You can also assign expiration dates and times for each tag or card, so you can easily control who has access at any given time. Vendors may need to enter the property for just a few hours, or a tenant may be moving out. These can be easily controlled with a credentialed visitor management solution.
6. Test the system
Don’t forget to test! Probe for vulnerabilities, test the readers and tags and make sure all doors are functioning properly. The last thing you want is for the system to malfunction when you need it the most.
Can RFID access be hacked?
Unfortunately, as technology has become more sophisticated, so have the ways bad actors attempt to access secured locations.
RFID is particularly vulnerable to hacking because it operates on radio waves, which can be intercepted with the right equipment. However, there are steps you can take to protect your system from these types of attacks.
-
- Make sure that all your readers and tags are secure and up-to-date
- Use encryption for wireless communications to prevent hackers from intercepting signals
- Combine with other access controls like biometrics or video monitoring
If you are looking for something even more secure, mobile authentication has become an increasingly popular option. It can utilize two-factor authentication, which requires an access code from the user’s phone to gain entry.
Smart cards, which have more computing power and data storage than regular RFID cards, offer another layer of security.
Source: Unsplash
RFID stickers for cars

Looking for something to control the entry of vehicles?
RFID Cards can be cumbersome when in a vehicle. The drivers has to fumble for their wallet or dig around in their center console for their card. Once they do they have to role down the window and try to wave the card in front of a card reader. Where RFID sticker transponders are completely passive. The driver doesn’t have to lift a finger.
RFID stickers for cars can be used to speed up the process at a gate or parking entrance. Stickers are placed on the car’s windshield or bumper, and when a vehicle approaches an entry point, it will scan the sticker and grant or deny access based on pre-set rules.
This is especially useful in large parking lots that require rapid entry/exit times.
The best RFID door locks for business
Sometimes, companies and property managers will try to buy the most inexpensive solution and end up with a system that doesn’t meet their needs.
The best RFID door locks for businesses will depend on the size and scope of your security needs. If you’re looking for something basic, an active or semi-passive system may be all you need. But if you want a more robust solution, look for
-
- Keyfobs or access cards that are durable and water-resistant
- An easy-to-use interface for programming tags or cards
- Multiple layers of authentication, such as PIN codes, biometrics, and encrypted data
- A system that is compatible with other security systems (if applicable)
Remember to always be looking forward. With technology constantly evolving, make sure you choose a system that can be upgraded as needed.

RFID Wired Locks vs Wireless Locks?
RFID locks come in two main varieties: wireless and wired.
A wired RFID lock connects to a power source and network through a physical cable. Because it is less susceptible to hacking and interference from other wireless devices, this type of lock is generally considered more secure. Furthermore, wired locks can be used to monitor and manage access control in real time, allowing administrators to see when people enter and leave a building. Wired locks, however, require running cables and may be more time-consuming and expensive to install.
Since they use radio waves to communicate, they are more susceptible to interference and hacking. To ensure security, you should choose a wireless lock that uses encryption and other security measures to prevent unauthorized access.
There is also a difference between the two types of RFID locks in terms of the range at which they can communicate with the access control system. A wired lock can communicate over a long distance, making it ideal for large buildings or complex systems. Because wireless locks have a limited range, usually around 30 feet, they are better suited to smaller areas or for adding access control to existing doors.
As a result of not requiring cabling, wireless locks are generally less expensive than wired locks. Depending on the features a wireless lock has and the level of security it provides, the cost will vary.
Wireless RFID locks or wired RFID locks will ultimately depend on the access control system’s needs and requirements. Although wired locks provide increased security and real-time monitoring, they are more expensive and take longer to install. Although wireless locks are more flexible and easier to install, they may be less secure and have a limited range. Before making a decision, it is important to consider the size and complexity of the access control system, the security requirements, and the budget.
Common use cases for commercial RFID locking systems
There are examples of RFID access control being used in a variety of commercial applications. From hospitals and office buildings to hotels and retail stores, RFID access control can be used to secure any facility or asset.
Here are some of the most common use cases.
RFID access for commercial office buildings
The most common use of RFID access control is in commercial office buildings. By having an automated system, businesses can ensure that only authorized personnel and visitors have access to the building during specified hours.
This eliminates the need for manual access checks and can help reduce security risks associated with human error.
Resorts and hotels RFID access
Establishments with a fast guest turnover rate need a reliable and efficient way to control access. RFID access control can be used to quickly grant guests access to their rooms and other areas of the property. It also eliminates the need for manual door locks, resulting in cost savings over time.
Plus, because of the inexpensive nature of RFID cards, they can be easily replaced if lost – something that happens quite frequently in hotels.
Residential community RFID access control
RFID access control solutions are also being used in residential communities such as gated neighborhoods, apartment complexes, and housing developments. With an RFID system, residents can quickly and easily gain entry to the community without having to fumble for keys or wait for a guard to open the gate.
Often, these will be more robust systems, incorporating multiple access levels with different restrictions for each.
Condominium RFID access
As the development of high-rise condominiums and apartments grows, so does the need for secure access control. RFID access control is an ideal solution for these types of buildings. It allows property owners to easily grant temporary or permanent access to visitors while maintaining a high level of security.
Vendors and service providers can also be given restricted access to certain areas of the building, keeping maintenance and construction out of residents’ way.
Benefits of using RFID access control
If you’ve used an RFID card before, you likely know just how smooth the process is. But what are the other benefits of using RFID access control?
-
- Ease of use: RFID access control requires no manual intervention. All users need to do is simply present their card or keyfob and the door will unlock automatically.
- Cost savings: By eliminating the cost of manual locks, keys, and other hardware, businesses can save a considerable amount of money over time. Additionally, installation costs are minimal compared to more traditional access control systems.
- Low maintenance: With RFID access control, there’s no need to manually check locks or replace batteries. All you have to do is ensure that the readers are in good working condition.
- Flexibility: RFID cards and keyfobs can be programmed with different levels of access rights, allowing businesses to configure their systems as needed.
- Analytics: RFID systems can also provide valuable insights into user behavior and access trends. This data can be used to improve security measures and make better decisions about who has access to certain areas of the building.
They can also offer a modern aesthetic to your access points, making them a worthy investment for both commercial and residential properties.
RFID access limitations
Before jumping into an RFID access control system, it’s important to consider the limitations of this technology.
Security
There are legitimate security concerns with RFID door entry systems. Criminals can use what are called “skimmers” to intercept the signal from an RFID card, print it onto a new card or fob, and gain access to the premises.
To combat this, it’s important to use RFID cards with high-security encryption and readers that are constantly updated with the latest software.
Identification
Think of the most basic RFID card you can – a hotel key for instance. When you swipe it in front of the door, nothing is confirming that you are the person authorized to access that space. You may be able to gain access without being identified, and if a criminal or unauthorized user were to get hold of your card, they’d also have access.
To resolve this issue, some RFID door lock systems use biometric identification as an added security measure. This requires users to provide their unique physical characteristics (like fingerprints) for the system to grant them access.
Tailgating
Another potential issue with RFID access control is known as “tailgating.” This occurs when a person follows an authorized user through an access point without having to present their credentials.
Many modern RFID systems come with anti-tailgating features, such as motion detectors that alert the system if more than one person passes through the door at once.
RFID Access Control Software
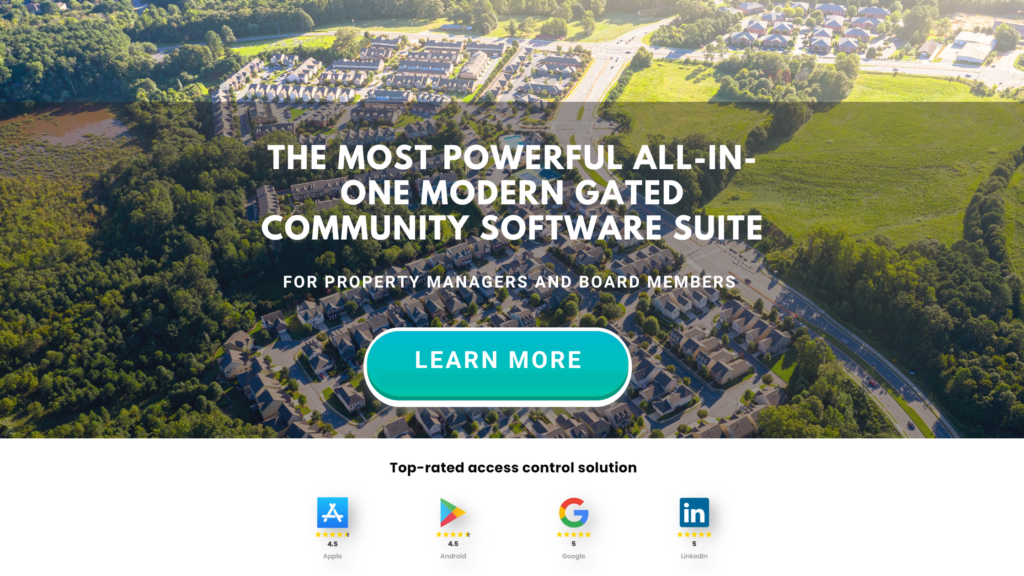
Now that you have an RFID Access Control System in place it needs to be managed. User data needs to be managed, credentialed and access levels need to be activated and deactivated, as well as you need to ability to easily define access levels and control your doors and gates. Well this is why it’s important to consider the software you are going to be logging into to manage this day to day. Many traditional access control solutions come with clunky and outated software interfaces that are difficult to learn and navigate. Where a more modern solution like Proptia’s Access Control module it modern, user-frieldny, extremely easy to navigate. It’s built so that someone with zero background in access control and get in there and effectively manage their security operations from any location.
Alternatives to RFID access control systems
RFID access control is not the only technology available. There are plenty of other options, each with its pros and cons.
Keypads
Keypad access control systems are a popular alternative to RFID. They require users to enter a numerical code into the keypad to gain access. While this system is cost-effective, it can be time-consuming and inconvenient for users who need frequent access.
Additionally, if codes are shared or forgotten, their security is compromised.
Biometrics
Biometric access control takes a different approach. It uses physical characteristics such as fingerprints, voice recognition, and facial recognition to identify users. This is more secure than RFID or keypad systems but can be expensive to set up and maintain.
Biometric data is also very sensitive and must be stored securely to protect user privacy.
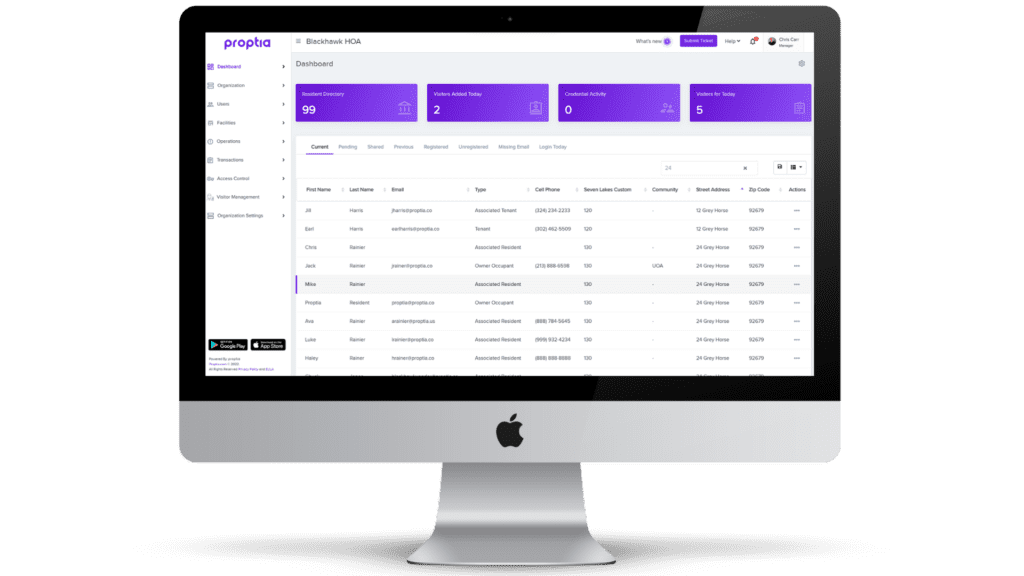
License plate recognition (LPR)
For vehicle entry, license plate recognition (LPR) is an effective option. It uses digital cameras to read the license plates of cars entering and exiting a property. While this system can be expensive, it offers a high level of security and convenience for drivers who need frequent access. Many can double as a visitor management system as well. Lastly, license plate recognition can serve as a reporting tool. High-end LPR systems are equipped to track vehicles make, model, color, and type as well as capture and store images of the vehicles coming and going.
Mobile credentials

Probably the fastest-growing alternative to RFID is mobile credentials. This technology uses a smartphone app to provide users with secure access. It has become popular in recent years due to its convenience, as essentially everyone carries a smartphone with them.
Many of the limitations of RFID are solved; mobile devices are much more difficult to clone, they are rarely lost or stolen, and they can include more identifying characteristics about the visitor or resident.
Real-time tracking of users is also possible with mobile credentials, providing an added layer of security.
Final thoughts
RFID is a great option for access control. It’s reliable, cost-effective, and easy to use. However, other technologies such as keypads, biometrics, LPR systems, and mobile credentials are becoming increasingly popular due to their improved security and convenience.
No matter what access control system you choose for your business or property, one thing is certain: it must be secure and reliable to protect against unauthorised entry. Contact Proptia today to find a solution that’s right for you.